Introduction
As Artificial Intelligence (AI) becomes increasingly embedded in organizational operations, the endpoint threat landscape continues to evolve. Endpoints are no longer limited to employee laptops and servers. They now include AI-assisted development environments, autonomous agents, virtual desktops, and unmanaged devices. These endpoints routinely access sensitive data. At the same time, attackers are adopting AI tooling to accelerate compromise, forcing security professionals to continuously evolve their practices to keep pace. This article examines how next-generation endpoint security addresses modern AI risks as a strategic necessity. It also provides insight into what security teams may still be overlooking as AI reshapes the attack surface.
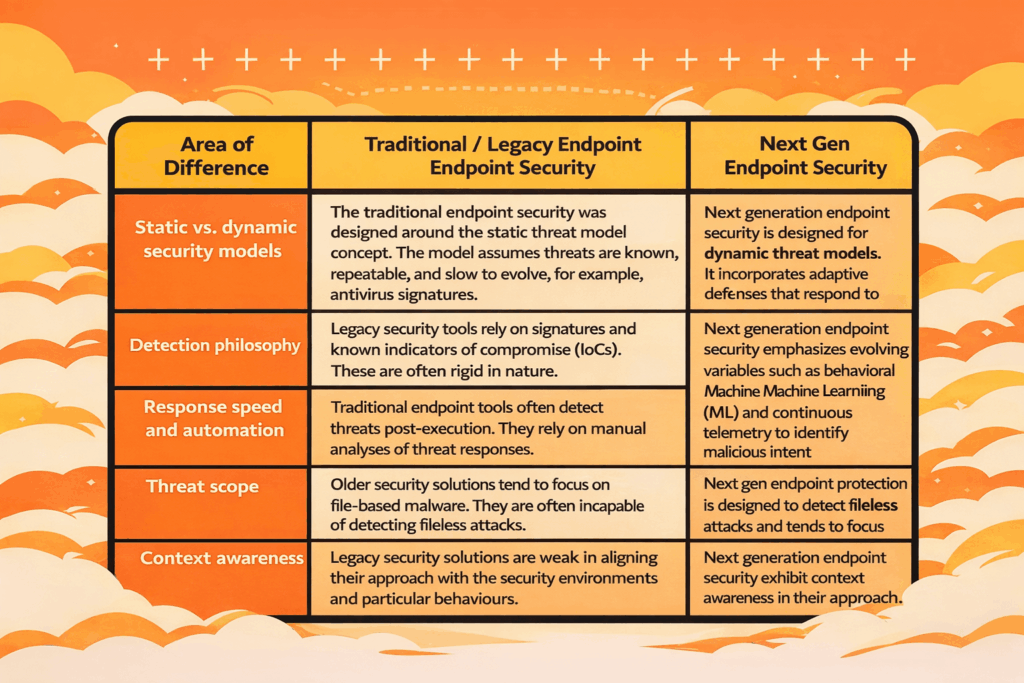
Key Differences Between Next Gen and Traditional Endpoint Security
There are several key differences between next-gen and legacy endpoint security that security professionals should be aware of, as shown in Table 1 below.
Table 1. Key Differences Between Traditional and Next Gen Endpoint Security
Why Modern Organizations Need Next Gen Endpoint Protection in 2026
In 2026, endpoints are expected to be the primary execution layer for AI-enabled work across most organizations. Software engineers and developers, for example, are increasingly using AI copilots, while business leaders and users are also interacting more with AI-driven Software-as-a-Service (SaaS) platforms through browsers and agents. This includes computer-use agents such as Claude Computer Use and OpenAI Operator. Each of these interactions has the potential to introduce new execution paths that legacy endpoint controls typically struggle to inspect and control. Reasons for this increased adoption of next-generation endpoint protection include:
- AI-accelerated attacks: Attackers can now leverage AI to automate aspects of attacks, including malware generation, phishing-to-endpoint workflows, and evasion testing. The challenge is that these attacks evolve faster than signature-based defenses can respond. As a result, they require proactive, machine-speed prevention capabilities to contain them, rather than traditional, often reactive methods
- Growth of unmanaged and semi-managed endpoints: Worldwide, there has been an increase in remote work and outsourced contractors. This has led to greater use of unmanaged and semi-managed endpoints across organizations. These endpoints often operate under strict Bring Your Own Device (BYOD) policies that limit centralized endpoint control. AI endpoint security incorporates effective behavior-based and risk-adaptive controls, even when full device management is not possible.
- Increased governance and board scrutiny: Boards and regulators are now stricter and expect demonstrable cyber resilience. A variety of regulations, including the US Health Insurance Portability and Accountability Act (HIPAA), the EU Artificial Intelligence (EU AI) Act, and other sector-specific requirements, now elevate endpoint security to a corporate governance priority. Endpoint compromise remains one of the main breach vectors in most organizations; as a result, it is now treated as a core element of enterprise risk management (ERM).
- Security team capacity constraints: The cybersecurity skills required to address the increased risk are in short supply. Most organizations face shortages of skilled security analysts, engineers, and other specialists. Next-generation endpoint security incorporates automation, reducing operational overhead through automated prevention and response.
Core Capabilities of Next Generation Endpoint Security Solutions
While many vendors market next-generation capabilities, security professionals need to evaluate these products for effectiveness and organizational fit. In general, the most effective next-generation endpoint security solutions consistently deliver the following:
- Behavioral and memory-level analysis: Modern next-generation endpoint platforms inspect runtime behavior, memory usage, and system calls. They do not rely solely on file inspection, though this may be part of the overall package. This combination is essential for detecting fileless malware and exploit-driven attacks in most organizations.
- ML-driven prevention: Next-generation endpoint solutions typically incorporate ML models. These models are trained on large datasets, enabling pre-execution blocking of unknown threats. This, in turn, significantly reduces reliance on reactive threat intelligence feeds and shifts security to a proactive posture.
- Integrated response and remediation: Modern platforms now integrate both response and remediation into a single platform. They often embed processes such as endpoint isolation, process termination, and rollback capabilities. This allows security professionals to support rapid incident containment without switching tools.
- Cloud-native analytics: Another key aspect of next-generation endpoint solutions is the use of cloud-native analytics. These solutions now incorporate cloud-based telemetry aggregation, enabling cross-environment correlation and continuous model improvement without overloading endpoint resources.
- Cross-platform support: Most organizations now operate in hybrid environments with a variety of systems. Next-generation endpoint solutions are system-agnostic and typically provide consistent protection across platforms, including Windows, macOS, Linux, and virtualized environments. This is key as enterprise environments continue to diversify across organizations.
How Next Gen Endpoint Protection Detects Unknown Malware and Zero-Day Attacks
A defining value proposition of next-gen endpoint security is its ability to prevent previously unknown threats, including zero-day attacks. This is particularly useful today, as AI enables rapid mutation of malware. Key detection techniques included in modern platforms include:
- Pre-execution analysis: Modern platforms now incorporate ML models that evaluate binaries and scripts before execution. This enables them to identify malicious characteristics without requiring signatures.
- Runtime behavioral monitoring: Leading platforms now include continuous monitoring capabilities. These can identify abnormal activities and other indicators, such as process chains, privilege escalation attempts, and suspicious system interactions, that are commonly used by zero-day exploits.
- Memory and exploit detection: Because zero-day attacks often execute entirely in memory, effective detection must identify exploit techniques and abnormal memory behavior rather than relying on known exploit code. This capability is built into next-generation endpoint solutions.
- Continuous learning loops: Next-generation endpoint solutions also incorporate cloud-based learning. This capability enables rapid adaptation to emerging attack patterns, which is critical in today’s AI-driven threat environment.
What Security Teams Are Still Missing
When deploying next-gen endpoint protection, it is important not to underestimate AI-related endpoint risks. Security teams often overlook the following during this process:
- AI tooling on endpoints: Security teams often overlook AI tooling on endpoints, including local models, AI plugins, and browser-based agents. Most of the time, these tools are left operating outside traditional security department visibility. They need to be explicitly accounted for across the organization to reduce security risks.
- Overreliance on malware detection metrics: Overreliance on malware detection metrics is another oversight on the part of many security teams. This phenomenon can obscure the abuse of legitimate tools such as PowerShell, Python, and related scripting tools and environments. The risk here is that such tools can also be used in modern attacks, which increases the risk level.
- Limited integration: The lack of full integration is particularly true between identity and zero-trust controls. This tends to weaken an organization’s endpoint defenses. In most cases, AI-enabled attacks pivot from endpoint access to identity compromise and data exposure. Security teams should therefore enforce tighter integration across all organizational control planes.
FAQs
What are some pitfalls when migrating from legacy to next-gen endpoint protection?
Common challenges in migrating from legacy to next-gen endpoint protection include insufficient policy tuning and underestimating the impact on users. Some security teams also expect immediate risk reduction without process changes. Successful migration requires phased deployment, clear governance processes, and effective alignment with existing incident response workflows.
How do next-gen endpoint protection solutions handle BYOD and unmanaged devices?
Most advanced next-generation threat security solutions use lightweight agents and browser-level controls. Though they also include risk-based access enforcement, they tend to focus on behavior and session risk rather than full device ownership. Some go a step further to integrate with zero-trust access principles to protect enterprise-wide data.
Are there performance benchmarks for next-gen endpoint tools across different OS?
Security solution vendors usually publish public security benchmarks for next-gen endpoint tools. However, the results of such benchmarks can vary depending on workload and configuration. Security teams should therefore validate performance through controlled pilots across various operating environments rather than relying solely on published metrics.
Conclusion
As detailed in this article, next-gen endpoint protection, including AI endpoint security, is no longer a simple exercise. It is increasingly about redefining endpoint trust in AI-driven environments. As attackers adopt AI to scale and accelerate threats, security teams should ensure their endpoint strategies meet organizational security requirements. Next-gen endpoint security solutions should be configured to prevent unknown attacks while supporting modern work patterns. For security leaders, the question is not whether to adopt next-gen endpoint solutions, but how to enhance them to effectively mitigate modern AI risks.
Useful References
- Trellix. (n.d.). What is next-gen endpoint protection? Trellix Security Awareness. https://www.trellix.com/security-awareness/endpoint/what-is-next-gen-endpoint-protection/
- Deep Instinct. (n.d.). Next generation endpoint security (NGES). Deep Instinct Glossary. https://www.deepinstinct.com/glossary/next-generation-endpoint-security-nges
- MITRE Corporation. (n.d.). ATT&CK® framework for enterprise. https://attack.mitre.org/
- National Institute of Standards and Technology. (2020). Zero trust architecture (NIST Special Publication 800-207). https://doi.org/10.6028/NIST.SP.800-207
- European Union Agency for Cybersecurity. (n.d.). ENISA threat landscape report. https://www.enisa.europa.eu/threat-risk-management/threats-and-trends