Software Supply Chain Attack: How the AI Agent Ecosystem Became a New Battleground
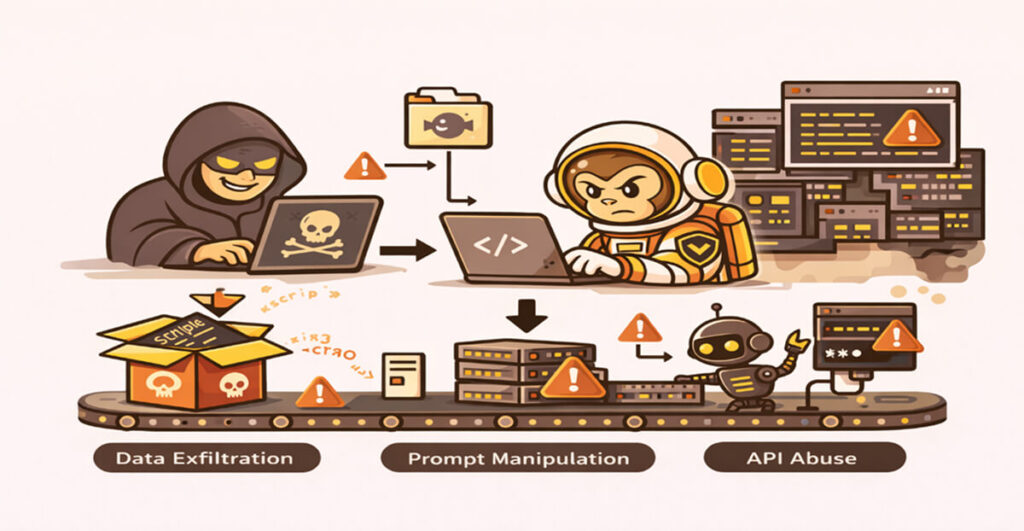
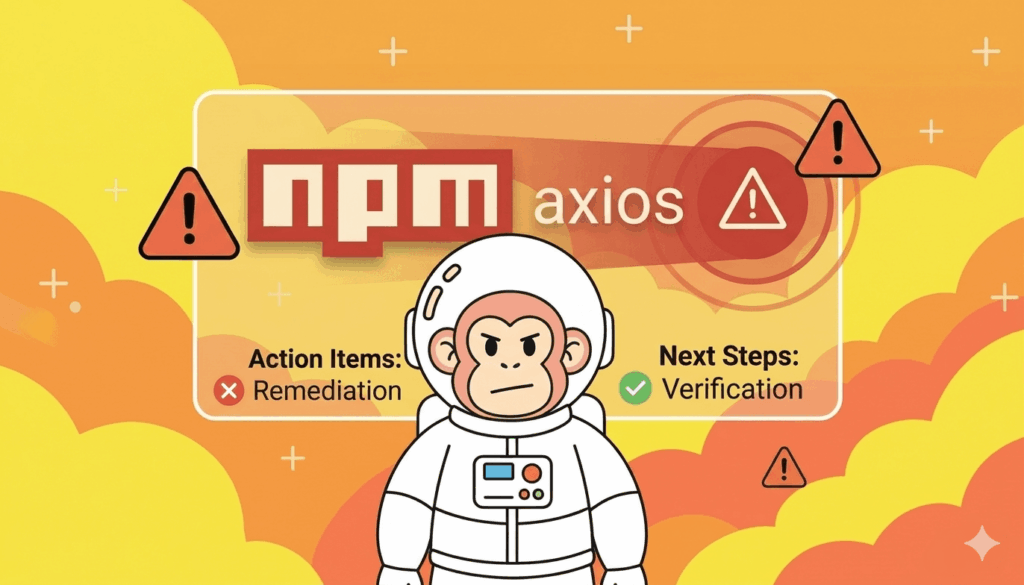
The software ecosystem has undergone a fundamental shift with the emergence of AI agents. Applications are no longer built from isolated codebases. They are now also developed from interconnected dependencies, automation tools, open-source components, and…