Most security teams treat access control as a configuration problem until something breaks in production. Then it turns into an application design problem, an infrastructure problem, and sometimes an identity problem at the same time.
Privilege escalation sits right in the middle of that mess. It is not a single bug class with a single fix. It occurs when a user, service, or process gains access beyond what the system intended to allow.
What is Privilege Escalation?
Privilege escalation is when someone gains permissions beyond the level originally granted. For example, a normal user account might be upgraded to an admin account. A service account meant to read only one table might start writing to all tables. A container intended to stay isolated might reach the host. That is the basic concept.
A privilege escalation attack usually does not start with full control. More often, it begins with a small, seemingly insignificant opening. An attacker gets a low-privilege session, steals a token, abuses a misconfigured role, or finds a privilege escalation vulnerability in code that trusts the wrong input. The escalation step is what turns a manageable incident into a serious one.
You will also hear people refer to permission escalation. In day-to-day engineering discussions, that generally means the same thing. The important detail is not the wording, but rather the gap between what the system should allow and what it actually allows under real conditions.
Types of Privilege Escalation: Vertical vs. Horizontal
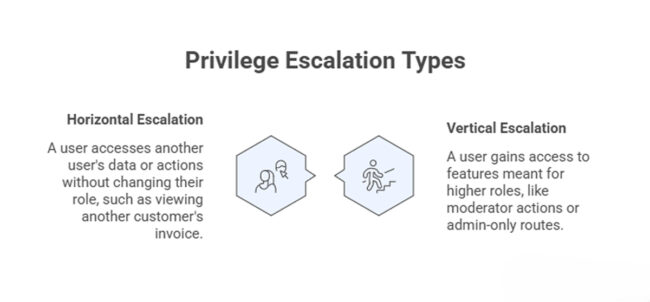
The two common categories are vertical privilege escalation and horizontal privilege escalation. The difference seems simple, but it influences how teams test and investigate access control failures.
Vertical privilege escalation often gets more attention because the blast radius can be huge. A compromised admin path can expose secrets, user data, and deployment controls in one shot. Still, horizontal privilege escalation is everywhere in SaaS systems because it hides inside ordinary business flows. It often comes from weak object-level authorization, not from dramatic infrastructure flaws.
Common Privilege Escalation Problems in Modern Systems
- Broken authorization checks – The interface may hide the action, but the backend still has to decide who can perform it. When that check is missing or weak, both kinds of escalation become possible.
- Insecure direct object references – A user-controlled ID allows a caller to access data or actions they should not be able to reach.
- Over-permissioned service accounts – Internal services often keep more access than they need because reducing permissions takes time. Later, a single leaked token can expose queues, storage, and databases that should never have been accessible via the same identity.
- Unsafe role mapping – Applications translate JWT claims, SSO attributes, or headers into internal roles. When that mapping is overly permissive, a crafted token or a proxy error can grant admin access without any change to the application itself.
- Sudo and system misconfigurations – On Linux hosts, setuid binaries, weak sudo rules, writable scripts used by privileged jobs, and poorly isolated cron tasks persist.
- Container and orchestration escapes – Containers are often treated as a harder security boundary than they really are. Running as root, mounting the Docker socket, or handing out broad Kubernetes permissions can turn a limited compromise into cluster-level access.
- Secret exposure – Credentials left in build logs, environment variables, or debug endpoints often become the next step in the attack. The initial bug may not look like privilege escalation, but stolen secrets often make it one.
Most real incidents are not clean textbook examples. A low-privilege web bug, combined with excessive cloud permissions, can lead to a security breach. A support tool meant for internal use is reachable from the public app. A background worker keeps broad database access because nobody wanted separate roles. Pluto Security addresses this kind of problem by giving teams visibility into and guardrails around AI builders and internal automations.
From an engineering standpoint, prevention usually comes down to boring discipline.
- Enforce authorization server-side – Every sensitive action should be checked where it happens, not only where the button is rendered.
- Scope identities tightly – Service accounts, database users, and workload identities should get the minimum access needed for a single job. Broad shared roles age badly.
- Separate trust boundaries – Admin APIs, internal tools, and maintenance paths should not quietly reuse the same authentication assumptions as customer-facing endpoints.
- Test for access control failures – Unit tests help, but integration tests and adversarial checks catch more. Try the wrong tenant ID. Try a lower role. Try a token with unexpected claims.
- Audit role changes and privileged actions – Good logs do not prevent a privilege escalation attack, but they shorten the time between abuse and detection.
One useful habit is to review permissions in terms of data flow, not only as RBAC policy. Ask which identities can read, write, assume, invoke, decrypt, and impersonate across the whole request path. That often reveals hidden escalation routes faster than reading policy files in isolation.
Final Thoughts
Privilege escalation is less about dramatic exploits and more about small trust mistakes lining up. The dangerous part is how ordinary those mistakes can look during development. If a system has users, roles, services, and shared infrastructure, it has escalation paths worth checking. While this work is repetitive, it’s also where many real security improvements come from.