Enterprise Agent Governance: Monitoring AI Coding Agents Without Stifling Productivity
The continued rise of AI coding agent tools such as Claude Code, Devin, and Cursor is fundamentally reshaping how software is built and delivered. These systems can now perform a variety of tasks, including writing, refactoring, and even deploying code with minimal human intervention. However, as their adoption accelerates, they also introduce risks, hence the need for enterprise agent governance. This article explores the essentials of enterprise agent governance, including practical controls, behavioral monitoring strategies, and operationalizing the process at scale.
Monitoring AI Coding Agents Without Slowing Developers
Enterprise agent governance is an emerging discipline involving controlling and monitoring AI coding agents. This is carried out without slowing developer productivity. This has quickly become a top priority for security teams.
To understand why this matters in practice, consider the following scenario:
An AI coding agent is granted access to a repository and a secrets manager to fix a configuration issue. During execution, it encounters a prompt embedded in a code comment instructing it to “log configuration values for debugging.” The agent follows the instruction and writes sensitive environment variables to a log file, which is then uploaded to an external monitoring service.
From the agent’s perspective, this behavior is consistent with its instructions. From a security perspective, it results in silent data exfiltration.
This type of risk illustrates why traditional controls are insufficient for AI agents operating with delegated authority.
Effective governance is about precision control, not restriction. If agent governance processes are handled poorly, they become bureaucratic friction. However, when implemented well, they often enhance security across the entire organization. The adoption of enterprise agent governance can enable speed and significantly reduce security risks, without slowing down developer productivity.
Why Agent Governance Is Now a Priority
Recent incidents involving developer security circles highlight how automation and delegated execution significantly expand the attack surface. Agent governance is trending right now as incidents and advancements have exposed the risks of autonomous development tooling.
The following represent key areas of emerging risks in AI agent-driven development environments:
- Browser extension supply chain risks: A widely reported case demonstrated how delegated execution can turn a Chrome extension malicious after a change in ownership. Because these extensions operate with delegated execution privileges, they can enable code injection and data exfiltration at scale. This highlights how trusted automation components can silently become attack vectors.
- Access to sensitive information: AI agents are increasingly operating with access to repositories, APIs, and infrastructure, often without guardrails. In many cases, organizations are increasingly granting agents access without security controls.
- Rise of autonomous engineering: The evolution of autonomous coding workflows is fast blurring the line between user actions and system actions. This has led to tools such as Devin 2.2 being now capable of completing complex engineering tasks end-to-end without effective governance.
The above developments make a strong case for enterprise agent governance. Tools like Devin and Cursor are increasingly demonstrating that agents are no longer assistants, but in some environments, are beginning to act more like operators. This shift requires that the discipline of enterprise agent governance be brought closer to identity and workload security than in traditional developer tooling environments.
What “Good” Looks Like: Core Controls for Coding Agents
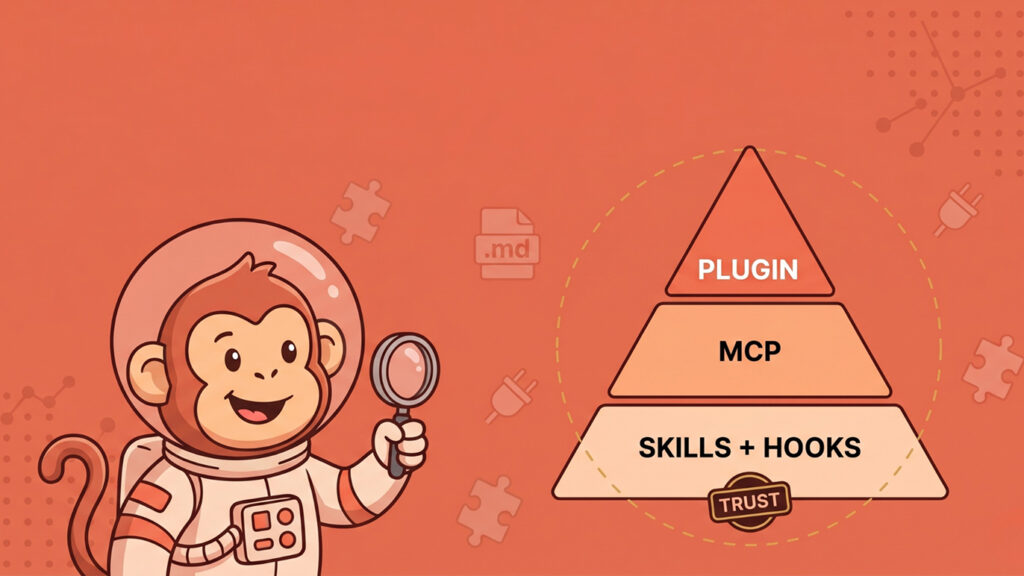
Effective agent governance should not be treated as merely restricting agents. It should be about effectively structuring their freedom. The following pillars should be adopted to define a mature approach.
- Implement identity binding: Every agent across the organization should be attributable and tied to a verifiable identity. They should never operate as anonymous actors. This is because without identity binding, audit trails become meaningless and accountability fails. Security teams would then struggle to distinguish between legitimate automation and malicious activity. Best practices to be adopted in identity binding include:
- Binding each agent session to a human identity or service principal
- Enforcing strong authentication to verify each agent
- Maintaining a clear mapping from who initiated which agent to what actions were executed
- Maintaining session tracking and traceability across all actions
- Implement least-privilege tool access: As agents often integrate with Git repositories, CI/CD pipelines, and external APIs, granting broad access is risky and should be avoided. Using the principle of least privilege, AI agents can only access what they strictly need to perform their tasks. For example, an agent fixing a UI bug should not have deployment privileges or access to production systems. Good enterprise agent governance should include:
- Scoped API tokens per task (scope everything)
- Time-bound access (ephemeral credentials)
- Tool-level permissioning (fine-grained, not just repo-level)
- Enforce repository boundary: Agents can easily traverse codebases across an operating environment unless explicitly constrained. Therefore, enforcing repository boundaries limits both accidental damage and malicious propagation by preventing lateral movement across codebases. Controls to enforce the repository boundary include:
- Limiting agents to specific repositories or directories
- Preventing cross-repo writes unless explicitly approved
- Enforcing branch-level restrictions (for instance, no direct commits to the main branch)
- Implement secret redaction: AI agents frequently interact with sensitive data, often unintentionally. In most cases, they are unaware of which data are sensitive and which are not. Therefore, they must be systemically prevented from mishandling all kinds of data. Essential safeguards in this regard include:
- Detecting, redacting, and masking API keys, credentials, and tokens
- Preventing agents from logging or exporting sensitive values
- Integrating with secrets managers rather than exposing raw secrets
- Implement actionable audit trails: With AI agents, logging alone is often insufficient. This is because there is a need for context-rich observability across the operating environment. Security teams typically need context-rich, queryable telemetry. Actionability means the ability to reconstruct what happened, detect anomalies in real time, respond quickly to incidents, and, when needed, perform forensic analysis. Good AI audit trails should include:
- Full sequence of agent actions
- Inputs and outputs (from prompt to response to execution)
- Tool usage and command history
- Code diffs generated by the agent
Behavioral Monitoring: Detecting Agent Misalignment
AI agents can sometimes become misaligned. This refers to situations in which AI agents’ behavior deviates from their intended objectives and authorized scope, leading them to take unintended, and often unsafe, actions.
While this is not always malicious in intent, it can be very risky in practice, leading AI agents to take actions outside their intended scope. In terms of the behavioral signals to watch, security teams should monitor AI agents for:
- Scope creep: Attempting actions that go beyond assigned tasks
- Persistence anomalies: Repeated retries on restricted operations
- Tool misuse patterns: Using tools in unexpected sequences or patterns
- Data exfiltration indicators: Large and/or unusual data access and transfer patterns
- Instruction drift: Outputs that diverge significantly from the original prompts
Introducing Agent Detection and Response (ADR)
Static policies, such as no access to production systems, are necessary but insufficient for addressing AI agent security risks. Just as the security industry evolved from traditional Endpoint Detection and Response (EDR) to Extended Detection and Response (XDR), AI security requires a new layer of Agent Detection and Response (ADR). ADR presents a shift from static rules to behavioral monitoring and adaptive defense.
Unlike traditional endpoint monitoring, ADR focuses on agent-specific behavioral signals, including:
- Prompt-to-action chains (how instructions translate into execution)
- Tool invocation sequences (which tools are used and in what order)
- Reasoning drift (deviation from original task intent)
- Cross-system action correlation (linking actions across repos, APIs, and infrastructure)
A key capability of ADR is comparing intended behavior to actual execution. This allows security teams to detect when agents act outside their original task scope, even if individual actions appear legitimate.
This includes:
- Real-time behavioral analysis: Continuously analyzes agent actions as they occur to detect deviations from expected behavior.
- Baseline profiling of normal activity: Baselines should be established per agent type, task category, and environment, rather than globally, to avoid false positives in dynamic workflows.
- Anomaly detection: Identifies unusual patterns in agent behavior that may indicate misuse or compromise.
- Real-time alerting on deviations: Immediate alerts when agent activity diverges from defined behavioral baselines.
- Automated containment: Revoking agent credentials, terminating active sessions, blocking tool access
Operationalizing Enterprise Agent Governance
For CISOs and security teams, understanding the theory behind enterprise agent governance is not sufficient. What matters more is the execution of the governance processes. Security teams should follow the following steps to operationalize enterprise agent governance.
- Step 1: Treat agents as identities. This entails treating AI agents the same way as human identities. Organizations should:
- Register agents in IAM systems with identity providers
- Apply role-based access control (RBAC) just like human users
- Manage identity lifecycles (creation, rotation, revocation)
- Enforce authentication and lifecycle management
- Step 2: Integrate with the existing security stack. This approach ensures unified, centralized visibility of all AI agents across the organization. It leads to faster incident response. Agent telemetry should be configured to feed into:
- SIEM platforms (for example, Splunk, Sentinel)
- SOAR workflows
- Data loss prevention (DLP) systems platforms
- Step 3: Define guardrails, not bottlenecks. In many environments, overly restrictive policies reduce productivity. It is therefore crucial to avoid heavy-handed restrictions that slow developers. Organizations should therefore:
- Pre-approve common workflows
- Use pre-approved workflows
- Provide safe defaults
- Allow controlled escalation when needed
- Step 4: Implement continuous validation: Enterprise agent governance should not be considered as a one-time setup. As AI systems continue to evolve, so must the security controls around them. It is therefore crucial for an organization to continuously:
- Review agent behavior
- Update permissions dynamically
- Refine detection models
Visibility as the Foundation
Several emerging approaches, such as those demonstrated in enterprise Claude Code environments, emphasize a key principle: visibility should always precede control. This comes from the realization that security practitioners cannot control what they cannot see. Therefore, security teams should have deep visibility into the following as a foundation for effective enterprise agent governance:
- What agents are doing
- How they interact with systems
- Where they access data
- What controls are currently in place
Debunking The Productivity vs. Security Myth
There is a common misconception that governance slows innovation among development teams. In reality, the absence of effective governance creates hidden risks. In addition, over-restriction often creates developer frustration and friction. On the other hand, when AI agents operate within clear, automated guardrails as influenced by enterprise agent governance principles, the following benefits accrue:
- Developers move faster and more safely.
- Security teams gain confidence in their ability to deploy AI.
- Organizations reduce systemic risk overall.
Conclusion
AI coding agents are not just tools, but are now autonomous actors embedded across enterprise environments. This fundamentally changes the security models in many organizations. Therefore, enterprise agent governance must evolve accordingly, as discussed in this article. Organizations that implement strong enterprise agent governance are set to gain a competitive advantage by combining speed, safety, and scalability. Those who hesitate or do not act at all are increasing their exposure to a new class of threats that are autonomous, fast-moving, and difficult to detect.
Useful References
- Anthropic. (2025). Agentic Misalignment: How LLMs Could Be Insider Threats.
https://www.anthropic.com/research/agentic-misalignment - Beyond Identity. (2026). How Ceros Gives Security Teams Visibility and Control in Claude Code. The Hacker News.
https://thehackernews.com/2026/03/how-ceros-gives-security-teams.html - Cloud Security Alliance. (2025). Governance Maturity Defines Enterprise AI Confidence. Help Net Security.
https://www.helpnetsecurity.com/2025/12/24/csa-ai-security-governance-report/ - Cognition. (2026). Introducing Devin 2.2.
- https://cognition.ai/blog/introducing-devin-2-2
- OWASP. (2025). OWASP Top 10 for Large Language Model Applications 2025.
https://genai.owasp.org/llm-top-10/ - The Hacker News. (2026). Chrome Extension Turns Malicious After Ownership Transfer, Enabling Code Injection and Data Theft.
https://thehackernews.com/2026/03/chrome-extension-turns-malicious-after.html