Building A Mythos-Ready Security Program
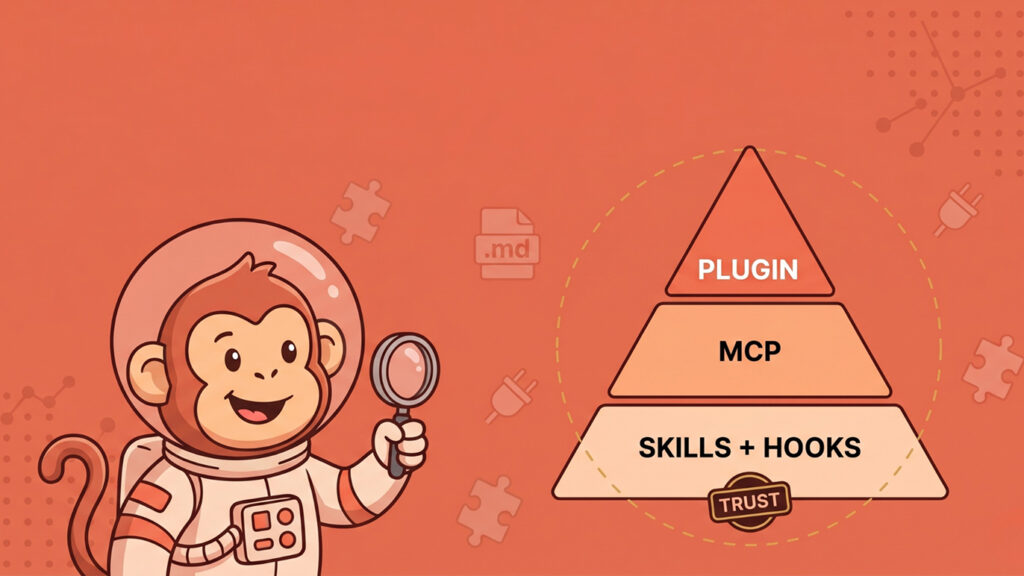
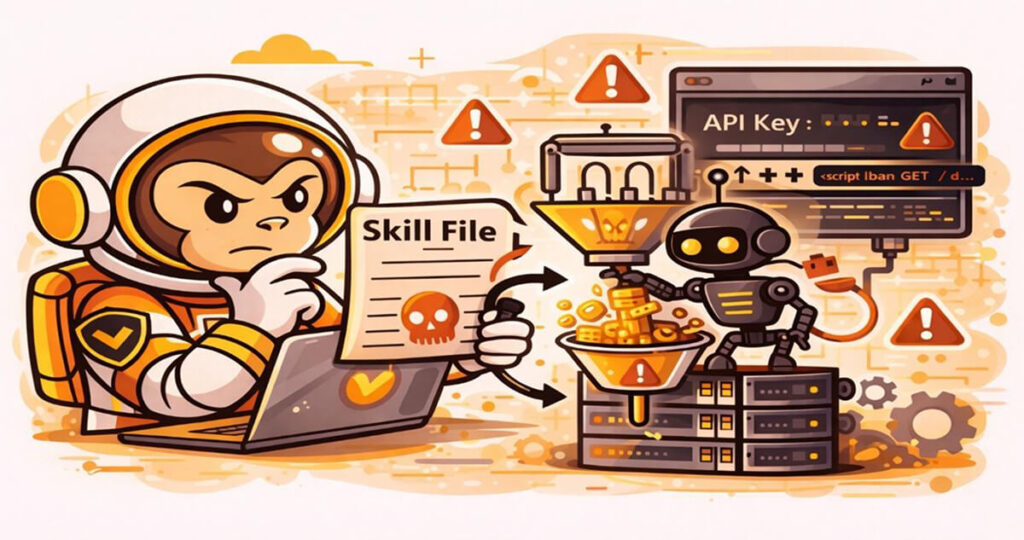
Building a Mythos-Ready Security Program: Key Takeaways from the field with Real-World Implementation As AI continues to reshape the cybersecurity landscape, the gap between vulnerability discovery and exploitation is shrinking rapidly across enterprises. The release…