Building a Mythos-Ready Security Program: Key Takeaways from the field with Real-World Implementation
As AI continues to reshape the cybersecurity landscape, the gap between vulnerability discovery and exploitation is shrinking rapidly across enterprises. The release of The AI Vulnerability Storm marks a structural shift in modern security operations, with AI significantly collapsing the time between vulnerability discovery and exploitation. A Mythos-ready security program is how organizations should respond to this new reality. It is not about adding more tools or controls but rather about building a unified security program that is adaptive and grounded in real-world threat dynamics. This article examines the key strategic and operational lessons emerging from this evolution and what security teams should do to adapt.
Key takeaways from the AI Vulnerability Storm publication:
AI agents are both a force multiplier and a security risk
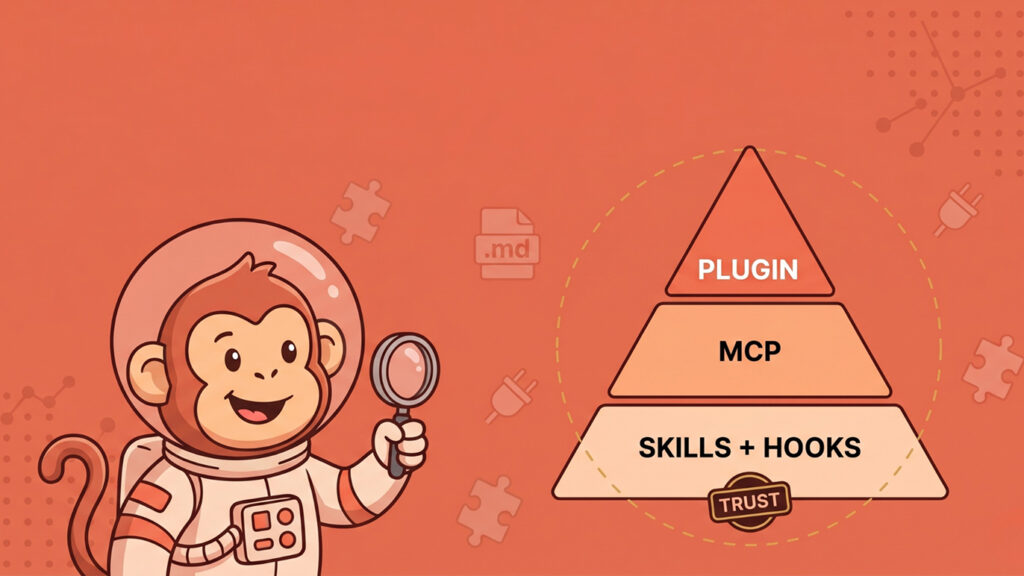
The report highlights the growing use of AI agents in enterprise environments. These AI agents are becoming even more privileged, inherently insecure, and beyond the oversight of traditional controls. Typical examples of emerging risks include prompt injection that eventually leads to data exfiltration, malicious plugins and MCP servers, and over-permissioned agents executing sensitive actions.
AI is both a security capability and an attack surface
As enterprises integrate AI into their operations, it is becoming a more powerful defensive tool, with security teams increasingly leveraging it in their defense operations. However, the same AI has also become a new attack surface. This duality significantly increases security risk and requires dedicated security controls.
Security fundamentals are no longer optional
In enterprise environments operating at AI speed, the security basics are not just important; they are mission-critical. Core practices such as asset inventory, patch management, network segmentation, and multi-factor authentication (MFA) have always mattered and remain crucial. While frameworks such as ISO/IEC 27001 and NIST CSF already emphasize these controls, implementation is often inconsistent.
Clarity beats complexity
One of the most overlooked principles in security design currently is simplicity. Complex frameworks, overlapping controls, and excessive documentation often create confusion, leading to gaps rather than resilience. The goal for security teams should be clear ownership, processes, and outcomes to enable everyone to understand how security works within the enterprise.
Asset inventory is static and not context-aware
The document highlights a fundamental reality: enterprises cannot secure assets they are not aware of. Traditional asset inventories are often static and unable to account for ephemeral cloud resources and other rapid changes, such as AI agents and shadow tooling. For example, in cloud environments, developers can rapidly deploy containers using CI/CD pipelines, much faster than traditional visibility mechanisms can track them. As a result, vulnerabilities are often missed.
Traditional risk models are becoming obsolete
The paper highlights that pre-AI assumptions about exploit timelines and remediation windows are no longer valid. For example, enterprises often assume in the traditional environment that the patch window can span 30 days without increasing risks. However, in AI environments, exploit weaponization can happen within hours. A growing asymmetry now is that while defenders operate at human speed, attackers operate at AI speed, rendering current risk models obsolete.
Compliance alone is not security
Passing audits does not necessarily mean that the organization is secure. Compliance frameworks are designed to provide assurance, and not to guarantee protection. However, most organizations continue to treat compliance as the end goal and focus on documentation rather than effectiveness, while ignoring the evolving AI threat landscape.
Security programs fail when they become fragmented
Most enterprises do not suffer from a lack of controls but a lack of integration. Over time, they adopt multiple frameworks, such as ISO/IEC 27001, SOC 2, and NIST CSF, each with its own structure, terminology, and audit requirements. The result is often a patchwork of duplicated controls leading to conflicting processes, disconnected tools, redundant controls, and audit fatigue.
Vulnerability chasing does not scale
One of the most strategic shifts is moving away from reactive security. Security teams often chase remediating individual vulnerabilities instead of focusing on misconfigurations, weak architectures, and poor development practices. Therefore, while AI increases vulnerability volume, fixing individual issues does not scale and becomes increasingly unsustainable.
Security solutions for real-world implementation
Security teams should adopt the Mythos-ready approach to address the above concerns as follows.
Turn AI inward: move from periodic testing to continuous adversarial simulation
This means that, technically, security teams should “fight fire with fire” rather than wait for defensive AI tools to mature, using the Mythos-ready approach to perform security functions. For example, an AI agent reviews pull requests, detecting insecure deserialization, identifying dependency vulnerabilities, and simulating exploit chains. This allows security to detect and remediate weaknesses before attackers can identify and exploit them.
Automate patch validation and deployment
Prioritize vulnerabilities based on exploitability, not CVSS, and accept operational downtime as part of the risk strategy. Leverage canary deployments with rollback AI-assisted patch, validation, and risk-based prioritization engine. This ensures rapid patch cycles and strong enforcement of controls across the environment.
Asset Inventory Must Become Dynamic and Context-Aware
As security teams cannot patch, segment, or defend what they do not know exists, the Mythos-ready solution is to perform continuous asset discovery via APIs, generate SBOMs for all builds, and undertake AI-assisted, real-time inventory classification.
Build a Dedicated VulnOps Function
The report suggests creating Vulnerability Operations (VulnOps) functions. These should operate as follows:
| Function | Description |
|---|---|
| Discovery | AI agent scans for and detects vulnerabilities and exposures |
| Triage | AI agent performs risk prioritization and suggests a patch |
| Remediation | AI agent deploys an automated patch |
| Validation | AI agent verifies fixes |
Rewrite Risk Models
As pre-AI assumptions about exploit timelines and risk are no longer valid, enterprises should design cyber risk models to reflect AI-driven attack models. It is also a plausible option to rewrite risk models. It is important to update metrics such as Mean Time to Detect (MTTD), Mean Time to Contain (MTTC), and the blast radius size to account for AI-driven automated exploitation.
Security teams must become ‘AI-enabled’
Security teams must evolve from being consumers of AI tools to AI-enabled roles such as the following:
Example:
| Role | Before | After |
|---|---|---|
| Analyst | Manually investigates alerts | Builds AI-assisted detection |
| GRC | Manually collects evidence | Automated compliance pipelines |
| AppSec | Manually performs reviews | AI-assisted code auditing |
Fix root causes, not just vulnerabilities
This aligns with a more mature, risk-based approach. As AI increases vulnerability volume, fixing individual issues does not scale-you need to fix the root causes. For example, instead of fixing 100 SQL injection vulnerabilities, just use AI to enforce a parameterized queries framework-wide, which is the root cause. This scales and improves long-term resilience.
Assume breach: engineer and design for containment and resilience
Modern enterprises always assume that, as a result of AI, incidents will no longer be rare, occur faster, and be even harder to detect in a timely manner. Hence, the principles of zero-trust should always be adopted in the Mythos-ready security program. Key technical mechanisms that can be adopted include:
- Microsegmentation (at the network and the workload level)
- Strong identity boundaries (per-service identities, short-lived tokens)
- Egress filtering to limit data exfiltration paths
- Enforcing MFA across all privileged access paths
- Implement just-in-time (JIT) access provisioning
Detection and response must operate at AI speed
The growing speed asymmetry between defenders operating at human speed and attackers at AI speed requires detection and operating at AI speed to level the playing field. For example, Mythos-ready SOC alerts should incorporate automated correlation to pre-authorized containment within seconds and incorporate AI-assisted triage and SOAR-driven response orchestration.
Secure AI as Both Infrastructure and Attack Surface
Security teams must treat AI systems as critical assets, potential entry points, and high-value targets. Responsible AI adoption should require the following:
- Securing AI models and pipelines
- Monitoring for misuse and abuse
- Enforcing model access controls
- Validating inputs and outputs
- Implementing audit logging
Move from fragmentation to unified security architecture
A Mythos-ready program brings everything together into one unified control framework. Controls are mapped across standards, with a single risk register and an audit-ready system. This centralized visibility improves governance, reduces duplication, costs, and effort, and aligns security with real-world threats rather than just audit requirements. It also creates a single source of truth for security across the enterprise.
Frequently Asked Questions (FAQs)
What does ‘Mythos-ready’ mean in cybersecurity?
A Mythos-ready security program is a unified, adaptive security architecture that is designed to align multiple frameworks into a single, coherent system. When designed effectively, it can autonomously identify and exploit vulnerabilities in real-time. This requires security teams to rethink and redesign their security programs to effectively handle this new reality.
How is this different from traditional compliance programs?
Traditional compliance programs primarily focus on passing audits rather than reducing real security risk. A Mythos-ready approach, on the other hand, goes further by ensuring security controls are operationally effective, risk-aligned, and continuously improved. This therefore shifts the objective ‘checking boxes’ to pass audits to actually reducing security risk across the enterprise.
Is Zero-Trust mandatory for a Mythos-ready program?
While not strictly mandatory for a Mythos-ready program, Zero-Trust principles are foundational for any modern security architecture, especially given the pervasiveness of AI threats. Security teams should therefore implement Zero-Trust principles to the extent possible. This is crucial in limiting lateral movement, enforcing identity-based controls, and reducing blast radius.
Are traditional frameworks still relevant?
Yes. Frameworks such as ISO/IEC 27001, SOC 2, and NIST CSF remain highly relevant in many enterprises. This is because they provide the foundation in this age of AI. However, they must be implemented in a way that reflects real-world speed and threat dynamics, not as a compliance checkbox.
Where should a company start becoming Mythos-ready?
Always start with establishing full asset visibility through:
- Strengthening core controls (patching, MFA, segmentation)
- Introducing AI-driven testing internally
- Unifying security and compliance efforts
- Building incident response readiness
Final Thoughts
The Mythos-ready shift represents a structural transformation in cybersecurity in the age of AI, and security teams should view it as a permanent change in how security works. A Mythos-ready program should be defined by continuous AI-driven testing, real-time asset intelligence, and automated remediation. A strong, unified containment architecture and adaptive controls should also be incorporated. Security teams should no longer aim to reduce every incident; instead, they should focus on reducing exposure by responding faster than attackers can escalate.
Useful References
- Cloud Security Alliance. (2026). The AI vulnerability storm: Building a Mythos-ready security program.
https://cloudsecurityalliance.org/artifacts/the-ai-vulnerability-storm/ - SANS Institute. (2026). AI and cybersecurity research and insights.
https://www.sans.org/ - OWASP GenAI Security Project. (2023). OWASP Top 10 for large language model applications.
https://owasp.org/www-project-top-10-for-large-language-model-applications/ - Evron, Gadi, Mogull, Rich, & Lee, Rob T. (2024). The AI vulnerability storm (contributor insights). Cloud Security Alliance. Retrieved from https://cloudsecurityalliance.org/artifacts/the-ai-vulnerability-storm/