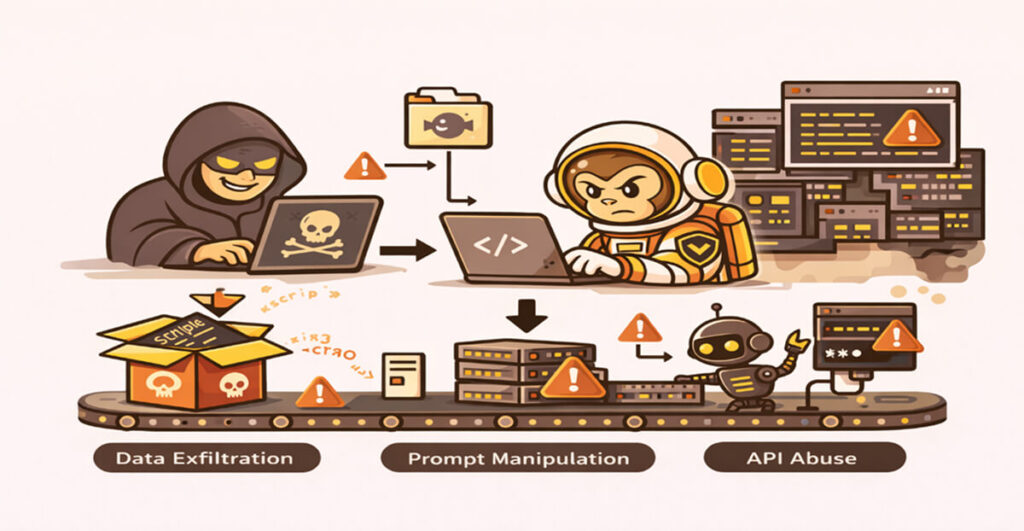
The Claude ecosystem has moved faster than the practical security guidance around it. Connectors, desktop extensions, managed agents, and new deployment surfaces are shipping weekly – and practitioners who want to adopt them responsibly are largely on their own when it comes to evaluating risk.
That gap is why we built ClaudeSec. It’s a free, community-oriented knowledge hub focused on one question: how do you use Claude and its surrounding tools safely? We’re launching today at claudesec.pluto.security, and it’s open to anyone.
Our thesis is simple. People want to adopt these tools. The AI capability curve is real, and teams are under pressure to move. But adoption without informed risk management is how incidents happen – and informed risk management starts with accessible, practitioner-grade knowledge. That’s what’s been missing for Claude specifically, and what ClaudeSec is trying to fill.
Connector and Extension Risk Database
The core of ClaudeSec is a searchable database of Claude connectors and desktop extensions. At launch we’re tracking 380 connectors, of which 142 are rated high risk, with 122 added in the last 30 days alone.
Each entry includes a capability matrix (shell execution, file access, outbound API calls, database queries, browser control, private data access, and more), a risk rating, a rationale, and the full tool list exposed to the model. Where it matters, we include source-code review findings.
A few concrete examples of what this looks like in practice:
– ToolUniverse presents itself as a science-catalog connector, but its implementation runs unsandboxed `exec()` over embedded tool source code and ships a `python_executor_tool` that runs arbitrary user code via `subprocess`. In effect, a Python runner wearing a science-catalog costume.
– Macos is described as “lightweight macOS desktop interaction.” The implementation is `subprocess.run(command, shell=True)` with zero filtering, no blocklist, and no sandboxing.
Neither of these is necessarily a tool you should never use – they’re useful in the right context. But if you’re deploying them inside an organization with sensitive data, you need to understand what they can actually do before you approve them, and the install page usually isn’t where that conversation happens.
Security Guides
Alongside the database, we’re publishing hands-on guides for deploying and operating Claude tooling safely. The first two – Claude Managed Agents and Claude Cowork – are live today. Additional guides like Claude Code or Claude Office Agents are in progress and will ship over the next several weeks.
Each guide is grounded in the actual configuration surface: policies, hooks, permission scopes, allow/deny rules, and the operational decisions that determine whether a deployment is safe in practice.
Latest Claude News
The Claude ecosystem moves fast, and so does the vulnerability and incident surface around it. The news feed on ClaudeSec curates disclosures, CVEs, policy changes, and releases that matter for security teams – the source map leak in v2.1.88, the April deny-rule bypass, the Claudy Day disclosures on claude.ai, and the cyber-filter over-blocking affecting vulnerability researchers are all on there, with our read on why each one matters.
Getting Involved
ClaudeSec is free, and we intend to keep it that way. The most useful thing you can do is subscribe – we’ll send new connector analyses, guides, and incident write-ups as they’re published.
If you have questions about specific deployment scenarios or want to discuss findings from our research in more detail, reach out to us at contact@pluto.security.